Simple Tips About How To Detect A Dos Attack
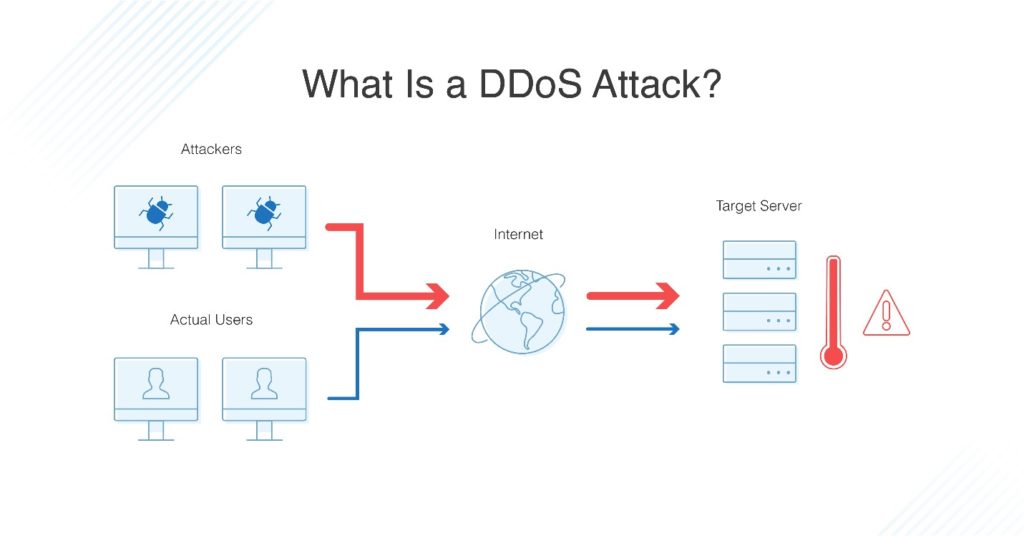
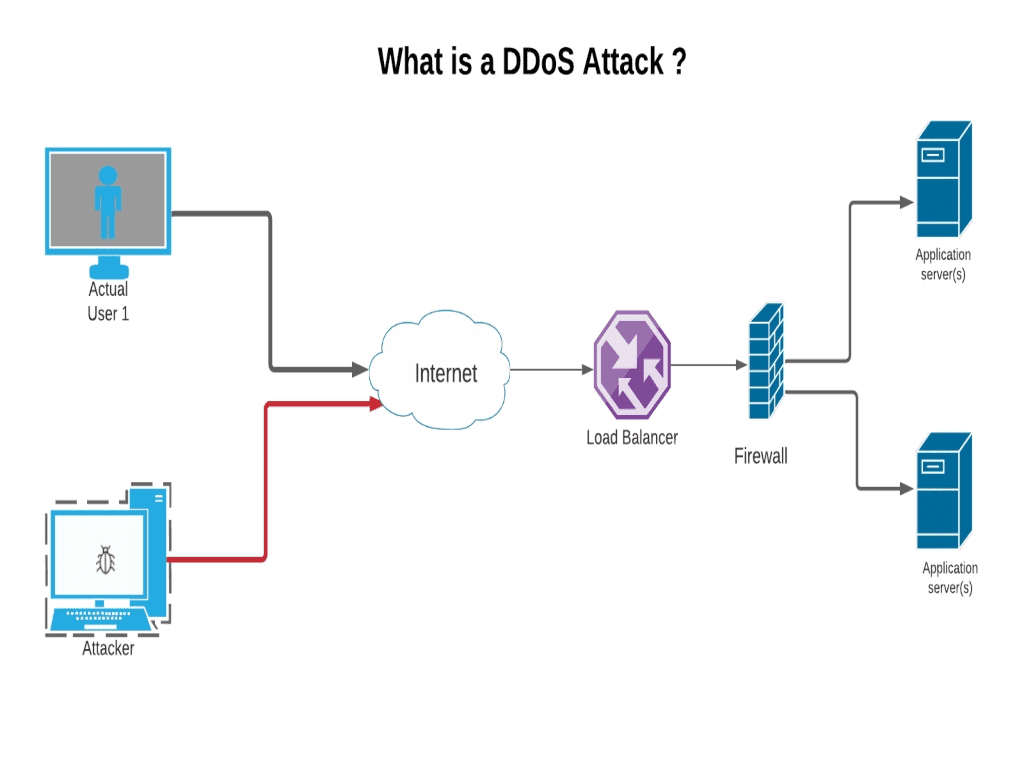
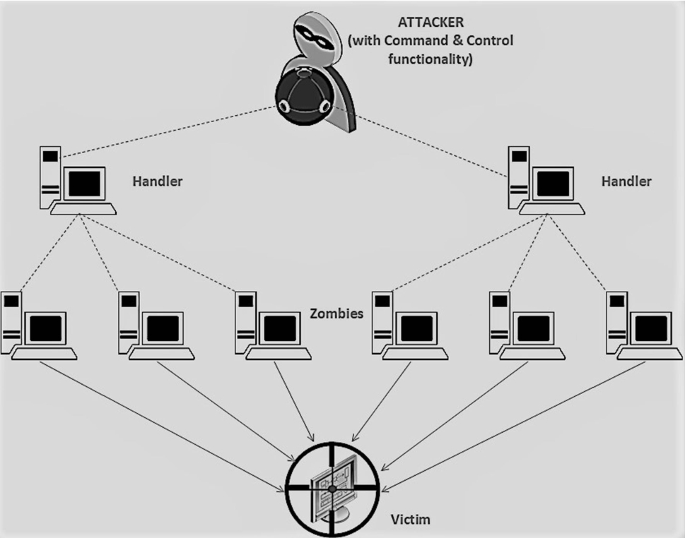
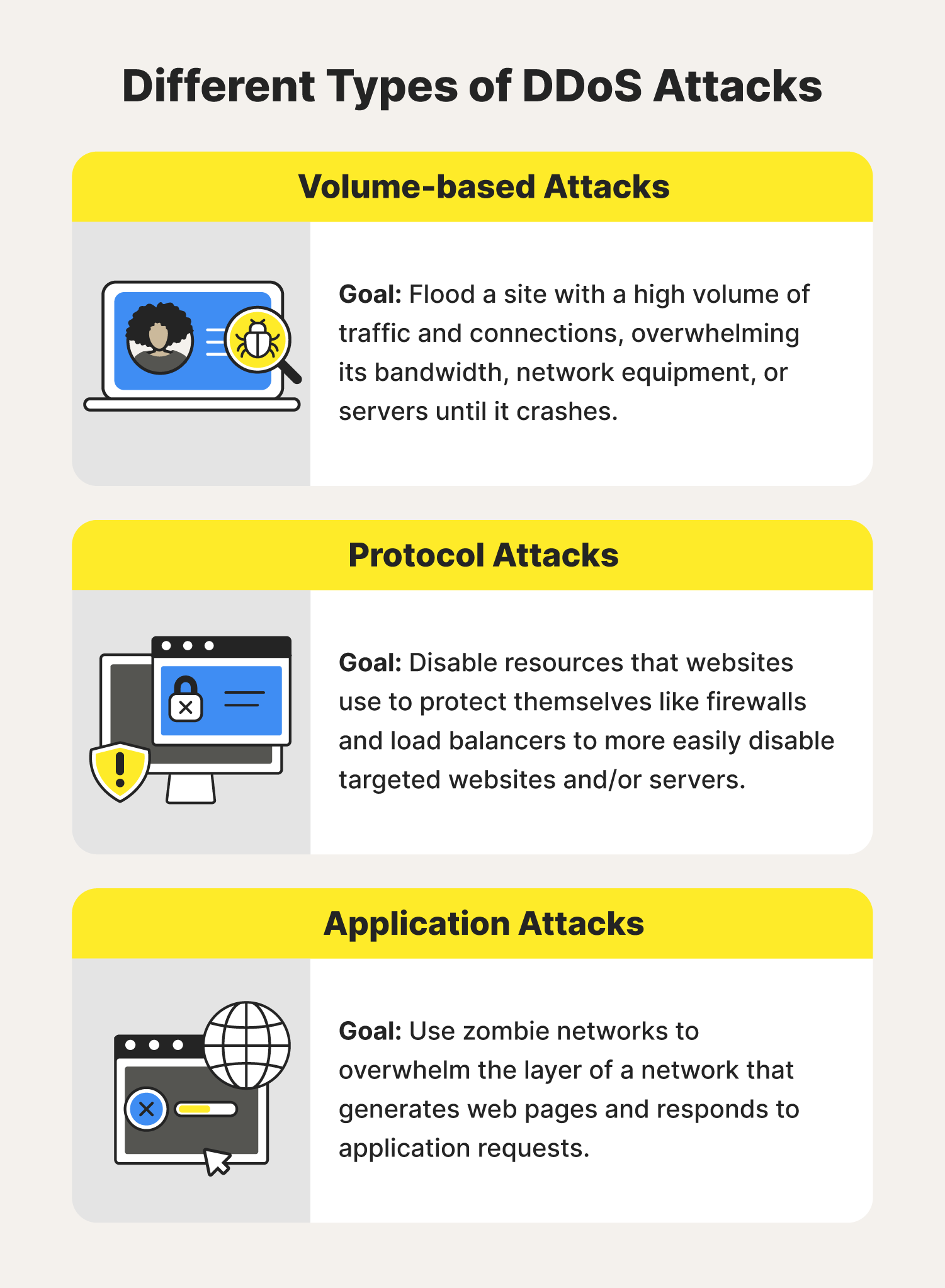
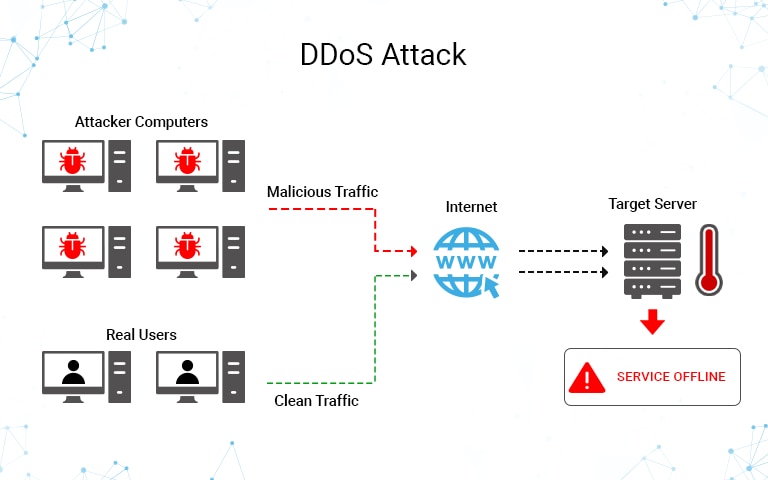
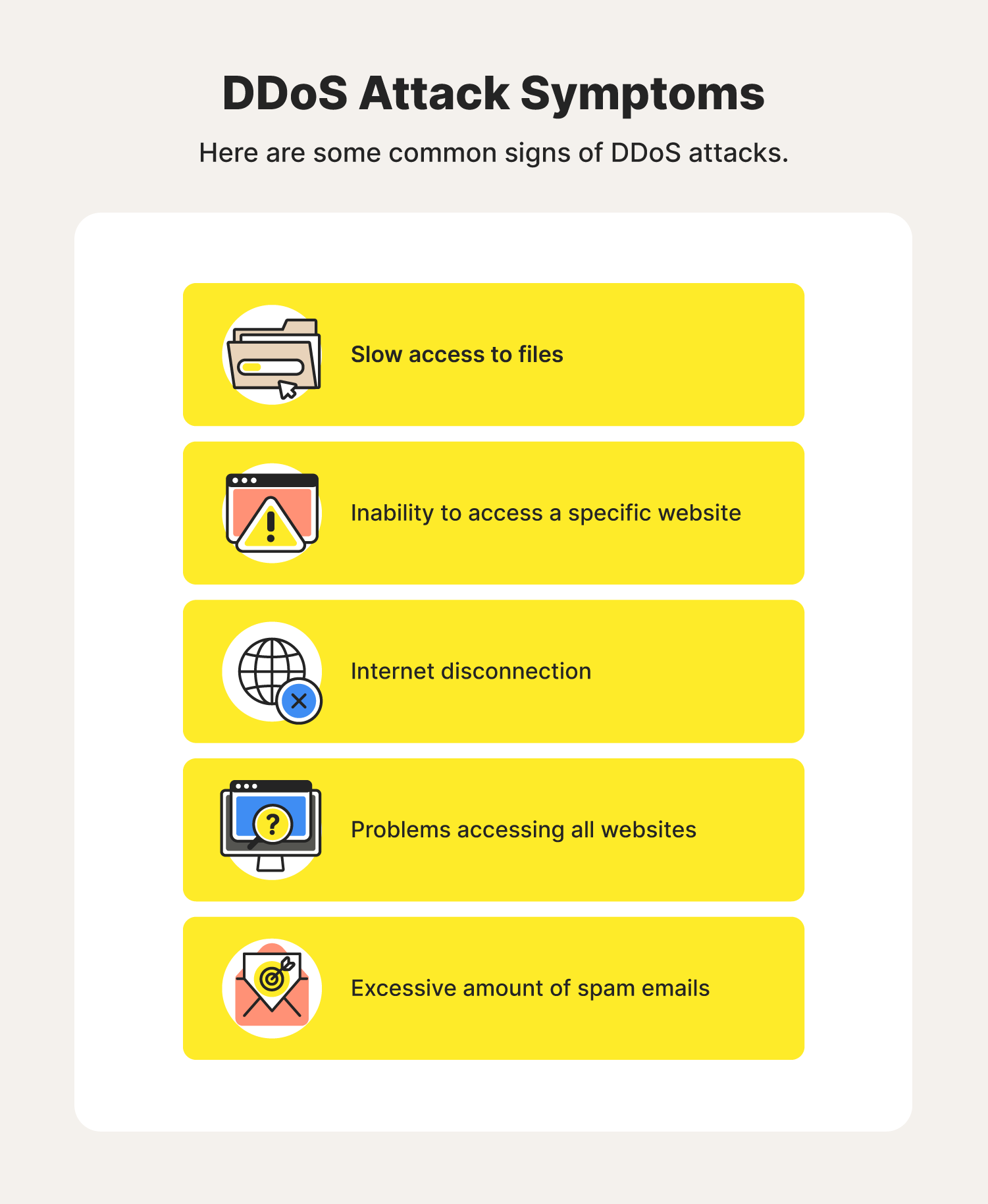
While there’s no one way to detect a ddos attack, there are a few signs your network is under assault:
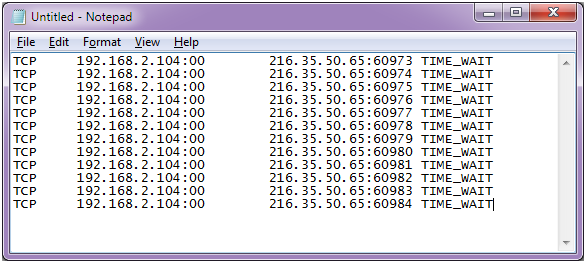
How to detect a dos attack. The first thing you will notice after the attack is server crashing. Open event viewer and right click on the event. Dns uses two types of packets:
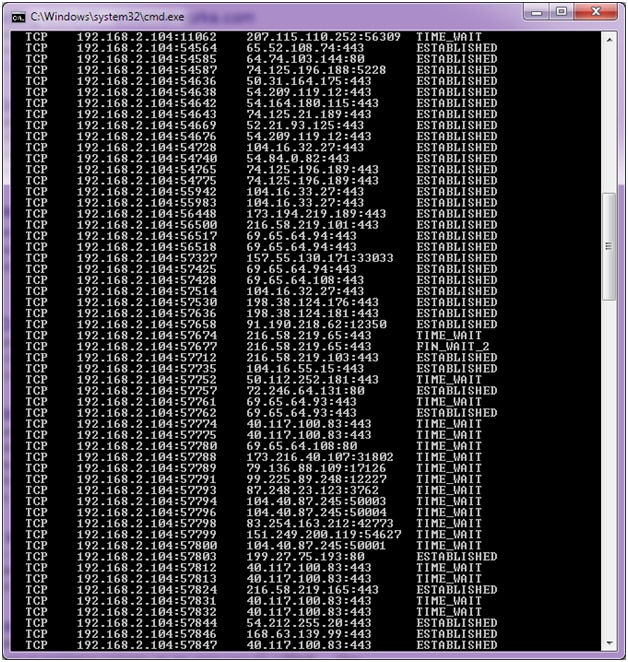
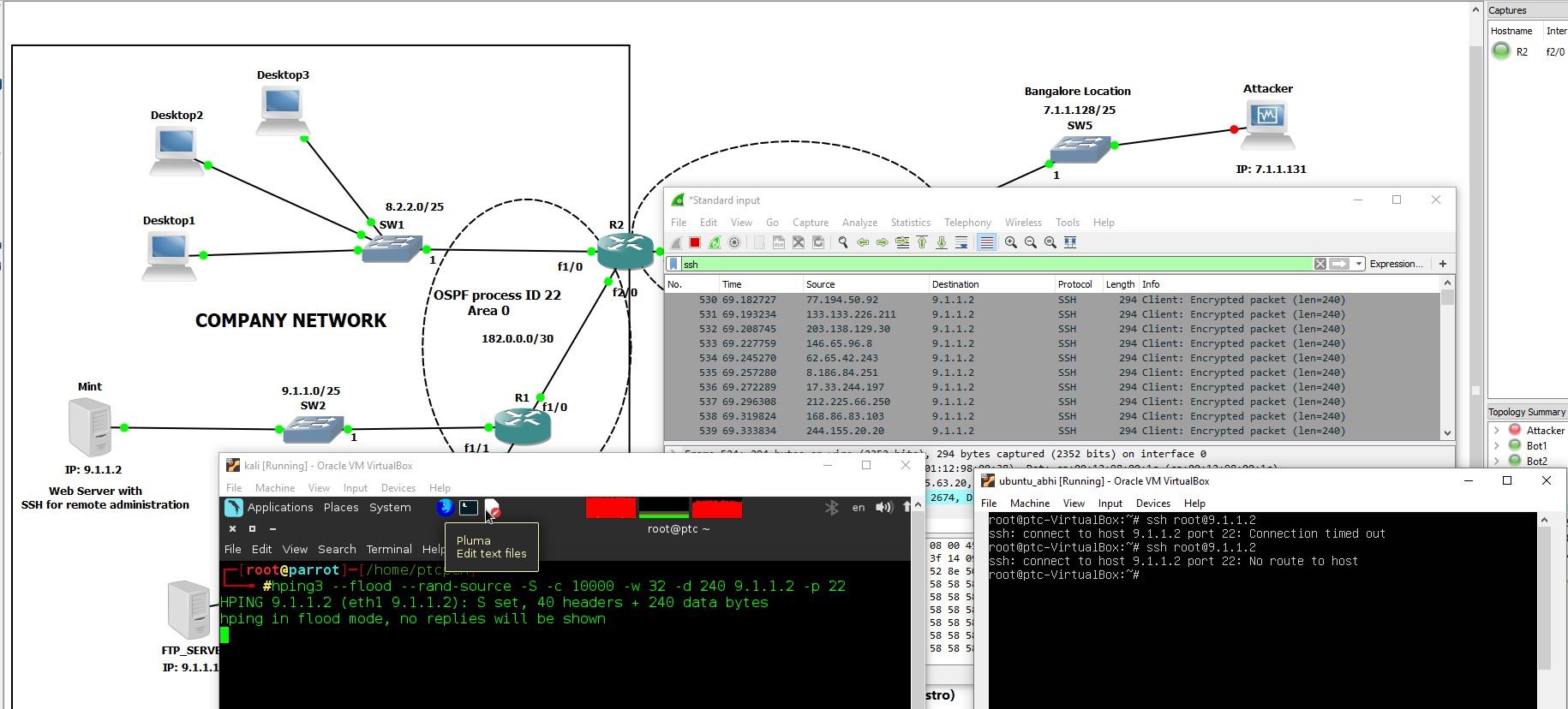
However, another sign of a ddos attack is a very strong spike in bandwidth. Early threat detection is the most efficient way to prevent a ddos attack. Monitoring dns activity is essential to identifying early signs of a dns flood ddos attack.
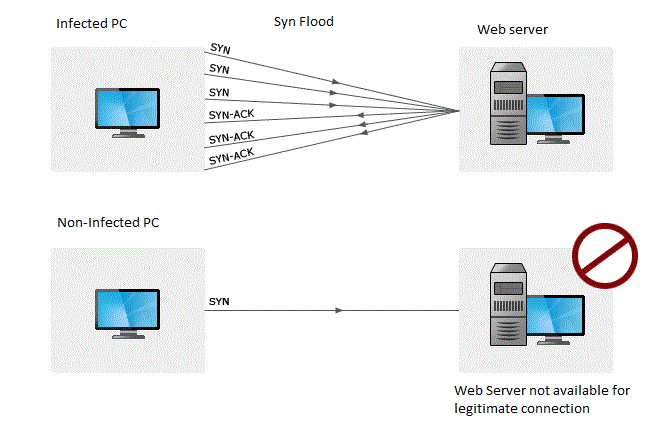
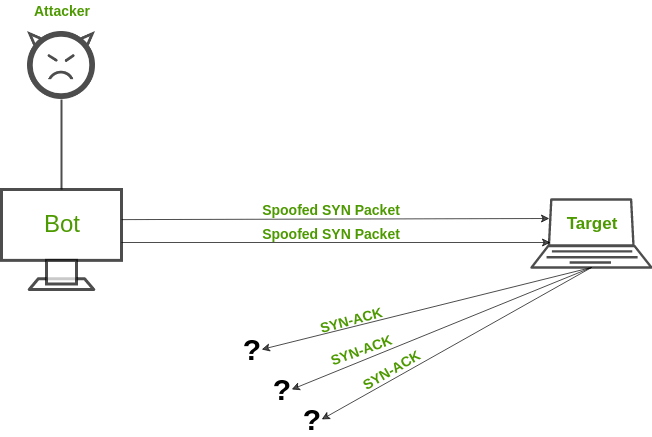
You see a surge in web traffic, seemingly out of nowhere, that’s coming from the. To learn how to create rules in the windows server to increase security against ddos attacks, pay attention to the following: Typically, these connections don’t get completed since.
An ip address makes x requests over y seconds your server responds with a 503 due to service. Wizard101 gear guide tippmann m4 carbine paintball gun. Who would i be in a horror movie buzzfeed x x
Certain ip addresses send too many connection requests over a short time. Even before you go and pull the server logs (more on that later) during a ddos attack, you’ll likely experience one or more of the following. Fill in the columns to send notification emails.
It can take hours to detect and mitigate a ddos attack at significant cost to the organization. You can view this by logging into your account with your web host and opening cpanel. The more you know about what normal inbound traffic looks like, the quicker you'll spot the start of a ddos attack.
Click server manager in the task bar. There are several clues that indicate an ongoing ddos attack is happening: A configuration screen will open.
You can also check your network stats and. How to detect a ddos attack. A graphical representation of the same is an easier way to understand abnormalities and guess a potential ddos attack.